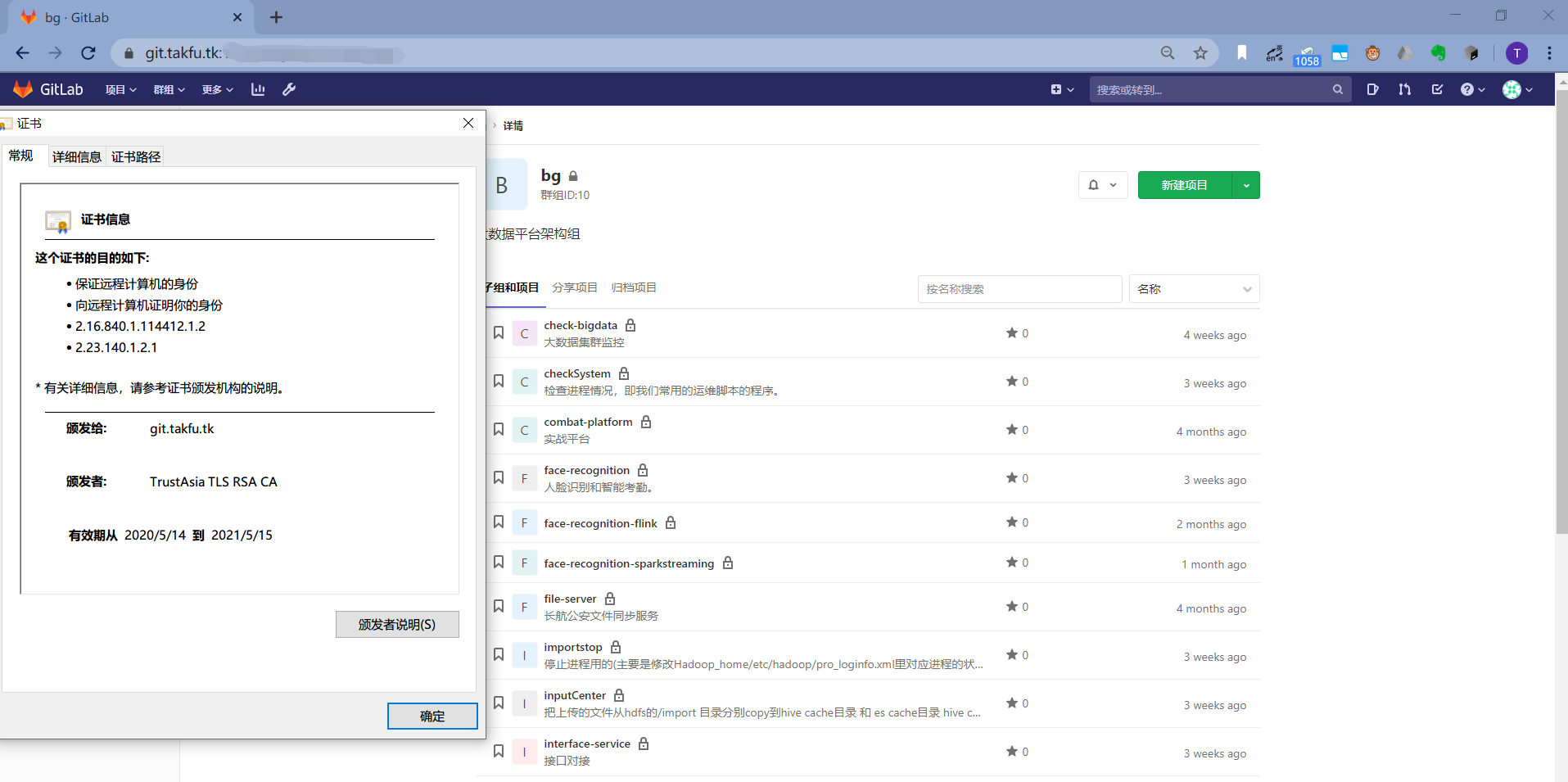
一份可使用 SSL 访问的gitlab-ce on docker 配置 。
直接上配置
/etc/gitlab/gitlab.rb
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20external_url = 'https://git.takfu.cf'
postgresql['enable'] = false # false,舍弃内置的pg,看自身情况
gitlab_rails['db_username'] = 'postgres'
gitlab_rails['db_password'] = 'yourpwd'
gitlab_rails['db_adapter'] = 'postgresql'
gitlab_rails['db_encoding'] = 'utf8'
gitlab_rails['db_host'] = '192.168.1.177' # 我使用的另外一个container跑了pg,原理一样,如果db在同一个container中,就用127.0.0.1
gitlab_rails['db_port'] = 15432
gitlab_rails['gitlab_shell_ssh_port'] = 1722 # ssh 自定义端口
unicorn['listen'] = '127.0.0.1'
unicorn['port'] = 8082
nginx['redirect_http_to_https']=true
nginx['redirect_http_to_https_port'] = 000 跳转https端口
nginx['listen_addresses'] = ['*']
nginx['listen_port'] = 82
nginx['ssl_certificate'] = "/etc/gitlab/ssl/git.takfu.cf.crt"
nginx['ssl_certificate_key'] = "/etc/gitlab/ssl/git.takfu.cf.key"
gitlab_rails['webhook_timeout'] = 90
gitlab_rails['git_timeout']=90
重新发布配置
1
gitlab-ctl reconfigure
/var/opt/gitlab/nginx/conf/gitlab-http.conf
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93server {
listen 443;
server_name git.takfu.cf;
ssl on;
ssl_certificate /etc/gitlab/ssl/git.takfu.cf.crt;
ssl_certificate_key /etc/gitlab/ssl/git.takfu.cf.key;
server_name git.takfu.cf;
server_tokens off;
client_max_body_size 0;
add_header Strict-Transport-Security "max-age=31536000";
add_header Referrer-Policy strict-origin-when-cross-origin;
access_log /var/log/gitlab/nginx/gitlab_access.log gitlab_access;
error_log /var/log/gitlab/nginx/gitlab_error.log;
if ($http_host = "") {
set $http_host_with_default "gitlab-gitlab-ce1";
}
if ($http_host != "") {
set $http_host_with_default $http_host;
}
gzip on;
gzip_static on;
gzip_comp_level 2;
gzip_http_version 1.1;
gzip_vary on;
gzip_disable "msie6";
gzip_min_length 10240;
gzip_proxied no-cache no-store private expired auth;
gzip_types text/plain text/css text/xml text/javascript application/x-javascript application/json application/xml application/rss+xml;
proxy_read_timeout 3600;
proxy_connect_timeout 300;
proxy_redirect off;
proxy_http_version 1.1;
proxy_set_header Host $http_host_with_default;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $connection_upgrade;
proxy_set_header X-Forwarded-Proto https;
location ~ (.git/git-receive-pack$|.git/info/refs?service=git-receive-pack$|.git/gitlab-lfs/objects|.git/info/lfs/objects/batch$) {
proxy_cache off;
proxy_pass http://gitlab-workhorse;
proxy_request_buffering off;
}
location /-/grafana/ {
proxy_pass http://localhost:3000/;
}
include /var/opt/gitlab/nginx/conf/gitlab-health.conf;
location / {
proxy_cache off;
proxy_pass http://gitlab-workhorse;
}
location /assets {
proxy_cache gitlab;
proxy_pass http://gitlab-workhorse;
}
error_page 404 /404.html;
error_page 500 /500.html;
error_page 502 /502.html;
location ~ ^/(404|500|502)(-custom)?\.html$ {
root /opt/gitlab/embedded/service/gitlab-rails/public;
internal;
}
}
server {
listen *:82;
server_name git.takfu.cf;
rewrite ^(.*)$ https://${server_name}$1 permanent;
}
server {
listen *:80;
server_name git.takfu.cf;
rewrite ^(.*)$ https://${server_name}$1 permanent;
}
/var/opt/gitlab/gitlab-rails/etc/gitlab.yml
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329gitlab:
host: git.takfu.cf
port: 17443
https: true
max_request_duration_seconds: 57
ssh_host:
ssh_user:
relative_url_root:
trusted_proxies:
user: git
time_zone:
email_enabled:
email_from:
email_display_name:
email_reply_to:
email_subject_suffix:
email_smime:
enabled: false
key_file: /etc/gitlab/ssl/gitlab_smime.key
cert_file: /etc/gitlab/ssl/gitlab_smime.crt
default_can_create_group:
username_changing_enabled:
default_theme:
issue_closing_pattern:
default_projects_features:
issues:
merge_requests:
wiki:
snippets:
builds:
container_registry:
webhook_timeout: 90
graphql_timeout:
repository_downloads_path:
impersonation_enabled:
usage_ping_enabled:
seat_link_enabled: true
incoming_email:
enabled: false
address:
user:
password:
host:
port:
ssl:
start_tls:
mailbox: "inbox"
idle_timeout:
log_path: /var/log/gitlab/mailroom/mail_room_json.log
artifacts:
enabled: true
path: /var/opt/gitlab/gitlab-rails/shared/artifacts
object_store:
enabled: false
direct_upload: false
background_upload: true
proxy_download: false
remote_directory: "artifacts"
connection: {}
external_diffs:
enabled:
storage_path: /var/opt/gitlab/gitlab-rails/shared/external-diffs
object_store:
enabled: false
direct_upload: false
background_upload: true
proxy_download: false
remote_directory: "external-diffs"
connection: {}
lfs:
enabled:
storage_path: /var/opt/gitlab/gitlab-rails/shared/lfs-objects
object_store:
enabled: false
direct_upload: false
background_upload: true
proxy_download: false
remote_directory: "lfs-objects"
connection: {}
uploads:
storage_path: /opt/gitlab/embedded/service/gitlab-rails/public
object_store:
enabled: false
direct_upload: false
background_upload: true
proxy_download: false
remote_directory: "uploads"
connection: {}
packages:
enabled:
storage_path: /var/opt/gitlab/gitlab-rails/shared/packages
object_store:
enabled: false
direct_upload: false
background_upload: true
proxy_download: false
remote_directory: "packages"
connection: {}
dependency_proxy:
enabled:
storage_path: /var/opt/gitlab/gitlab-rails/shared/dependency_proxy
object_store:
enabled: false
direct_upload: false
background_upload: true
proxy_download: false
remote_directory: "dependency_proxy"
connection: {}
terraform_state:
enabled:
storage_path: /var/opt/gitlab/gitlab-rails/shared/terraform_state
object_store:
enabled: false
remote_directory: "terraform_state"
connection: {}
registry:
enabled: false
host:
port:
api_url:
path:
key: /var/opt/gitlab/gitlab-rails/etc/gitlab-registry.key
issuer: omnibus-gitlab-issuer
notification_secret:
sentry:
enabled: false
dsn:
clientside_dsn:
environment:
mattermost:
enabled: false
host:
pages:
enabled: false
access_control: false
path: /var/opt/gitlab/gitlab-rails/shared/pages
host:
port:
https: false
external_http: null
external_https: null
artifacts_server: true
gravatar:
plain_url:
ssl_url:
sidekiq:
log_format: json
cron_jobs:
stuck_ci_jobs_worker:
cron:
expire_build_artifacts_worker:
cron:
environments_auto_stop_cron_worker:
cron:
pipeline_schedule_worker:
cron:
repository_check_worker:
cron:
admin_email_worker:
cron:
personal_access_tokens_expiring_worker:
cron:
repository_archive_cache_worker:
cron:
ci_archive_traces_cron_worker:
cron:
pages_domain_verification_cron_worker:
cron:
pages_domain_ssl_renewal_cron_worker:
cron:
pages_domain_removal_cron_worker:
cron:
schedule_migrate_external_diffs_worker:
cron:
geo:
node_name:
registry_replication:
enabled:
primary_api_url:
feature_flags:
unleash:
enabled: false
url:
app_name:
instance_id:
gitlab_ci:
all_broken_builds:
add_pusher:
builds_path: /var/opt/gitlab/gitlab-ci/builds
ldap:
enabled: false
sync_time:
prevent_ldap_sign_in: false
host:
port:
uid:
method:
bind_dn:
password:
active_directory:
allow_username_or_email_login:
lowercase_usernames:
base:
user_filter:
group_base:
admin_group:
sync_ssh_keys:
sync_time:
smartcard:
enabled: false
ca_file: "/etc/gitlab/ssl/CA.pem"
client_certificate_required_host:
client_certificate_required_port: 3444
required_for_git_access: false
san_extensions: false
kerberos:
enabled:
keytab:
service_principal_name:
use_dedicated_port:
port:
https:
omniauth:
enabled:
auto_sign_in_with_provider:
allow_single_sign_on: ["saml"]
block_auto_created_users:
auto_link_ldap_user:
auto_link_saml_user: null
external_providers: null
allow_bypass_two_factor: null
providers:
shared:
path: /var/opt/gitlab/gitlab-rails/shared
gitaly:
client_path: /opt/gitlab/embedded/bin
token: ""
repositories:
storages: {"default":{"path":"/var/opt/gitlab/git-data/repositories","gitaly_address":"unix:/var/opt/gitlab/gitaly/gitaly.socket"}}
backup:
path: "/var/opt/gitlab/backups" # Relative paths are relative to Rails.root (default: tmp/backups/)
archive_permissions: # Permissions for the resulting backup.tar file (default: 0600)
keep_time:
pg_schema:
upload:
connection:
remote_directory:
multipart_chunk_size:
encryption:
encryption_key:
storage_class:
pseudonymizer:
manifest:
upload:
remote_directory:
connection: {}
gitlab_shell:
path: /opt/gitlab/embedded/service/gitlab-shell/
hooks_path: /opt/gitlab/embedded/service/gitlab-shell/hooks/
authorized_keys_file: /var/opt/gitlab/.ssh/authorized_keys
upload_pack:
receive_pack:
ssh_port:
git_timeout: 10800
git:
bin_path: /opt/gitlab/embedded/bin/git
monitoring:
unicorn_sampler_interval: 10
ip_whitelist:
- "127.0.0.0/8"
- "::1/128"
sidekiq_exporter:
enabled: true
address: 127.0.0.1
port: 8082
web_exporter:
enabled: false
address: 127.0.0.1
port: 8083
shutdown:
blackout_seconds: 10
prometheus:
enable: true
listen_address: "localhost:9090"
extra:
rack_attack:
git_basic_auth:
admin_area_protected_paths_enabled:
development:
<<: *base
test:
<<: *base
gravatar:
enabled: true
gitlab:
host: localhost
port: 80
repositories:
storages:
default: { "path": "tmp/tests/repositories/" }
gitlab_shell:
path: tmp/tests/gitlab-shell/
hooks_path: tmp/tests/gitlab-shell/hooks/
issues_tracker:
redmine:
title: "Redmine"
project_url: "http://redmine/projects/:issues_tracker_id"
issues_url: "http://redmine/:project_id/:issues_tracker_id/:id"
new_issue_url: "http://redmine/projects/:issues_tracker_id/issues/new"
jira:
title: "JIRA"
url: https://samplecompany.example.net
project_key: PROJECT
ldap:
enabled: false
servers:
main:
label: ldap
host: 127.0.0.1
port: 3890
uid: 'uid'
method: 'plain' # "tls" or "ssl" or "plain"
base: 'dc=example,dc=com'
user_filter: ''
group_base: 'ou=groups,dc=example,dc=com'
admin_group: ''
sync_ssh_keys: false
staging:
<<: *base
- sshd_config
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27# 在centos中需要自己开启sshd
Port 22
ChallengeResponseAuthentication no
HostKey /etc/gitlab/ssh_host_rsa_key
HostKey /etc/gitlab/ssh_host_ecdsa_key
HostKey /etc/gitlab/ssh_host_ed25519_key
Protocol 2
PermitRootLogin no
PasswordAuthentication no
MaxStartups 100:30:200
AllowUsers git
PrintMotd no
PrintLastLog no
PubkeyAuthentication yes
AuthorizedKeysFile %h/.ssh/authorized_keys /gitlab-data/ssh/authorized_keys
AuthorizedKeysCommand /opt/gitlab/embedded/service/gitlab-shell/bin/gitlab-shell-authorized-keys-check git %u %k
AuthorizedKeysCommandUser git
# Fix: User username not allowed because account is locked
# With "UsePAM yes" the "!" is seen as a password disabled account and not fully locked so ssh public key login works
UsePAM yes
# Disabling use DNS in ssh since it tends to slow connecting
UseDNS no
# Enable the use of Git protcol v2
AcceptEnv GIT_PROTOCOL
重启gitlab
1
gitlab-ctl restart
查看下日志有无Error
1
gitlab-ctl tail
解决500问题
1
2
3
4
5
6
7
8gitlab-rails console
# 1.将配置中的token加密重置
settings = ApplicationSetting.last
settings.update_column(:runners_registration_token_encrypted, nil)
# 2.如果还未能解决,针对每个groupId中的token配置进行重置
Namespace.find_by_full_path('<groupId>').update(runners_token: nil,runners_token_encrypted: nil)
- 访问页面



能否参与评论,且看个人手段。